Looking for a way to login to your Linux server via SSH without specifying a password? Using an SSH key pair is the way to go then. If done properly, this results in more convenience for you and more security for your server. In this article you’ll learn step-by-step how to setup an SSH key pair for logging into your server via SSH, without having to enter a password.
Background
SSH stands for Secure Shell Protocol. SSH makes it possible for you to open up a remote terminal session on your server. More importantly, it does so while using a cryptographic based communication protocol. This means that all communication between your PC and your server is secure, even over an unsecured network. Consequently, SSH is the ideal method for remotely administering a Linux server.
After you setup Linux on your server, the installer probably already installed the OpenSSH server software. With OpenSSH running on your server, you can login to your server with the ssh program, using command syntax:
ssh [USERNAME]@[HOST] -p [PORT]
Replace [USERNAME] with the username of your user account on the server. Next, replace [HOST] with its IP-address, hostname or fully qualified domain name. The -p [PORT] part can be left out, if you use the default port 22, otherwise replace [PORT] with the SSH port you configured on the server. Example:
ssh pragmalin@www.example.com
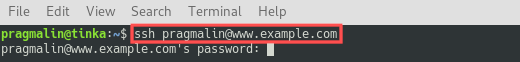
After running the ssh command to remotely login to your server, you need to enter your password in order to establish the connection. This makes sense, yet also poses a security threat. Especially with an Internet facing server, someone will figure out its IP address and try to login via SSH by guessing a username and password combination. With enough persistence and patience, they might eventually succeed.
What if I told you that it’s possible to login via SSH without a password and at the same time close this security threat? So increased convenience for you and increased security for your server. The trick is to use an SSH key pair, instead of a password. In this article I’ll explain how you can configure SSH to login with the help of an SSH key pair.
What do you need
This article assumes you already run a Linux server somewhere with:
- A user account setup that has sudo access.
- OpenSSH running such that you can remotely login via SSH.
The server can be a VirtualBox virtual machine, a cloud server or even a Raspberry PI. In case you quickly want to setup such a server, follow the instructions in one of these tutorials:
- Debian server installation in VirtualBox
- Setup a minimal Debian server as a Linode VPS
- Perform a minimal install on your Raspberry PI
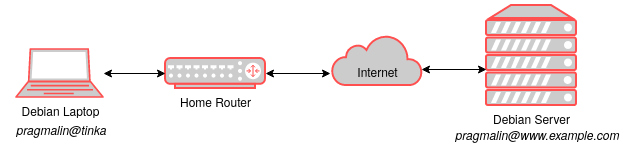
My system setup for this article consists of my Debian laptop (tinka) and a Debian server with www.example.com as the fully qualified domain name:
What is an SSH key pair?
An SSH key pair essentially consist of two files that belong together. One is called the public key and the other one the private key. This key pair forms a unique combination, with its contents based on hard to crack cryptography. Think of the SSH key pair as a key and lock system, as illustrated in the following image:
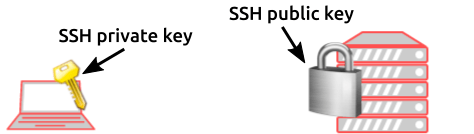
Others might find your server, but only you have the SSH private key on your PC. Therefore, only you can unlock access to your server via SSH. As the name implies: do not share the private key with anyone else.
Generate an SSH key pair
Now that we know what an SSH key pair is, it’s time for the next step for making it possible to login via SSH without a password. This step involves the actual creation of the SSH key pair. So afterwards we should end up with two files:
- The private SSH key file, which we later on register on our own PC.
- The public SSH key file, which we later on store on our server.
On a Linux system, you can find SSH keys in the .ssh directory of your home folder. Before we generate the SSH key pair, we first make sure that this directory exists and set it as the current directory:
mkdir ~/.sshcd ~/.ssh
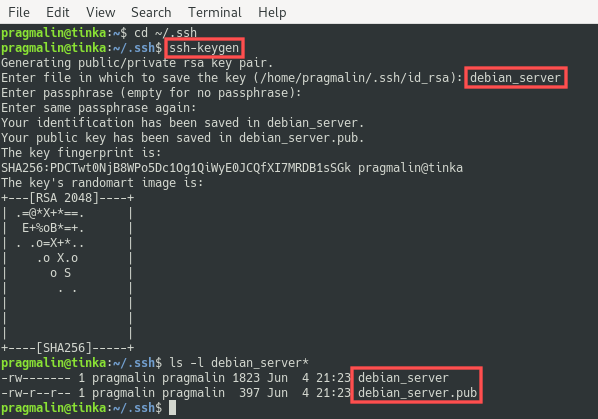
From the .ssh directory, start the SSH key pair creation process by entering command:
ssh-keygen
The program prompts you to enter a file name for the key pair. In this example I specify debian_server as the name, but you can change this to whatever name you prefer. Next, the program prompts you for a passphrase. This is a text string of your choice that you would need to enter each time you use the key for authentication purposes. For convenience you can leave the passphrase empty by simple pressing Enter twice. You now have a brand spanking new SSH key pair. The private key file is called debian_server and the public key file is called debian_server.pub:
Register the private SSH key on your PC
With the SSH key pair in place, we are one step closer to setting things up for logging into SSH without a password. The next step involves registering the private SSH key file on our PC. Think of it as attaching the new key to your key-chain.
Before registering the private SSH key file, open the terminal and verify that the SSH authentication agent is actually running. Next, register the private SSH key file with the help of the ssh-add program:
eval "$(ssh-agent -s)"
ssh-add ~/.ssh/debian_server
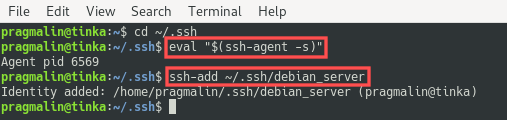
Setup of the private SSH key file on your own PC is now done. Note that if you ever need to unregister the private SSH key file from the authentication agent, you can do so with the same command and specifying the -D option: ssh-add -D ~/.ssh/debian_server.
Copy the public SSH key to the server
You only need to complete one more step, before you can login to your server over SSH, without specifying a password. This step involves copying the public SSH key file over to your server. Think of it as installing the lock on your server.
The program ssh-copy-id assists with this step. Assuming that your working directory is set to ~/.ssh, the command syntax is:
ssh-copy-id -i [PUBLIC SSH KEY FILE] [USERNAME]@[HOST]
So in my case:
ssh-copy-id -i debian_server.pub pragmalin@www.example.com
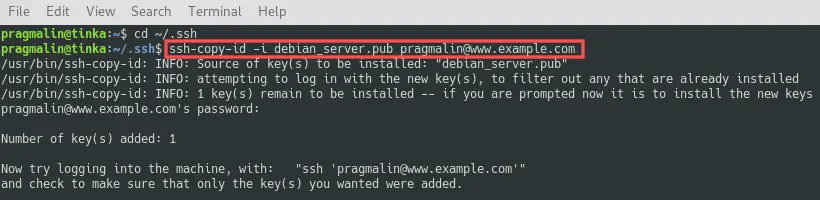
This adds the public SSH key file to ~/.ssh/authorizedkeys on your server.
Login via SSH without using a password
At this point we prepared everything and it should be possible to login our server via SSH, without entering a password. Let’s give it a try. You can use the usual command for connecting to the server via SSH, so
ssh [USERNAME]@[HOST]
For my server the command is:
ssh pragmalin@www.example.com
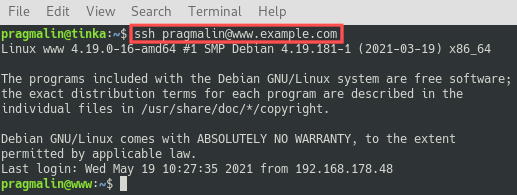
As you can see in the screenshot, I was able to login via SSH without being prompted for a password. This proves that the new SSH key pair works.
Further SSH security hardening
In the previous steps, we managed to setup an SSH key pair, which enables us to login to our server without specifying a password. We can further improve the server’s security by:
- Disabling the root user from logging in.
- Completely disabling password authentication, since we don’t need it anymore.
To proceed with these steps, connect to your server via SSH and edit file /etc/ssh/sshd_config, for example using the Nano terminal editor:
sudo nano /etc/ssh/sshd_config
Next, make sure that the following variables are set to no:
PermitRootLoginPasswordAuthenticationChallengeResponseAuthentication
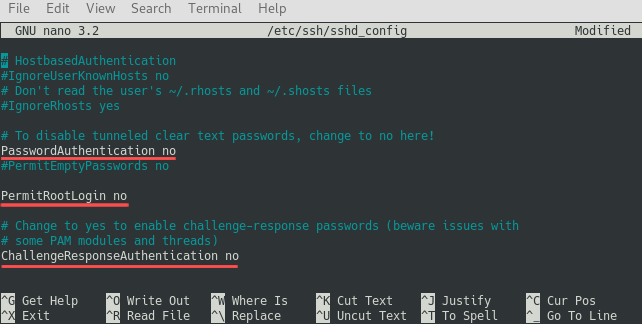
Next, save the changes to the file and exit the Nano editor. As a final step, restart the SSH server to activate the new configuration settings:
sudo service ssh restart
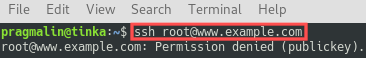
That’s it. It is now impossible for the root user to login via SSH. All other users can login, but only with an SSH key pair. No longer with a username and password. Here’s what happens if someone tries to login as the root user now:
Wrap up
This article explained step-by-step how you can configure the SSH connection with your server, such that you can login without a password. We achieved this with the help of an SSH key pair. Not only does this give you more convenience, but also more security. We completed the following steps:
- Generated the SSH key pair.
- Registered the private SSH key on your PC.
- Copied the public SSH key to the server.
Now that the SSH login without a password works, we performed some extra SSH security hardening on your server by disabling password authentication altogether. While we were at it, we disabled the root user from logging in as well.
With these measures in place, you no longer have to worry about unwanted third parties gaining access to your server via SSH. They will still try though. To further discourage them from such SSH brute force attacks, you could consider installing Fail2ban.